Приветствую.
Имеется роутер Keenetic Giga (KeeneticOS: 3.8.5). На роутере поднята служба SSTP Server, и есть два пользователя для неё.
Есть ли возможность сделать так, чтобы у первого vpn пользователя был доступ и к локальной сети роутера и к Интернету, а у второго пользователя закрыть доступ к локалке, чтобы он мог ходить через VPN лишь в Интернет?
У клиентов VPN статические адреса, я пытался в разделе «Межсетевой экран», сделать запрещающее правило для своей локальной сети 192.168.21.0/24 со статического адреса VPN клиента, но это не работает. Я добавлял это правило на интерфейс «Подключение Ethernet» и «Домашняя сеть». Почему-то отдельного интерфейса для SSTP не появляется, как у других vpn соединений, например WireGuard появляется отдельная вкладка (видимо потому что в них я клиент, а не сервер).
Я менял сеть для SSTP на Гостевую, и хотел сделать первому пользователю разрешающее правило в домашнюю сеть. Но это то же не работает. Или все клиенты ходят только в интернет или все и в локалку и в интернет.
Может кто-то сталкивался с подобной необходимостью? Прошу вашей помощи.
Сообщение от insect_87
Экспорт так и не показали
Кликните здесь для просмотра всего текста
# apr/21/2022 14:32:01 by RouterOS 6.48
# software id = 3QMP-QT9G
#
# model = RouterBOARD 750G r3
# serial number = 6F3806A8C7D1
/interface bridge
add admin-mac=6C:3B:6B:C2:3F:CF auto-mac=no fast-forward=no name=LAN
/interface ethernet
set [ find default-name=ether2 ] name=LAN1 speed=100Mbps
set [ find default-name=ether3 ] name=LAN2 speed=100Mbps
set [ find default-name=ether4 ] name=LAN3 speed=100Mbps
set [ find default-name=ether5 ] name=LAN4 speed=100Mbps
set [ find default-name=ether1 ] mac-address=EC:43:F6
100Mbps
/interface list
add name=»INT LAN»
add name=»INT WAN»
/interface wireless security-profiles
set [ find default=yes ] supplicant-identity=MikroTik
/ip pool
add name=dhcp_pool1 ranges=192.168.1.100-192.168.1.248
add name=vpn-pool ranges=192.168.7.2-192.168.7.254
/ip dhcp-server
add address-pool=dhcp_pool1 authoritative=after-2sec-delay disabled=no \
interface=LAN lease-time=10h10m name=dhcp1
/ppp profile
add bridge=LAN change-tcp-mss=yes local-address=192.168.7.1 name=VPN only-one=\
no remote-address=vpn-pool use-compression=yes use-encryption=yes use-mpls=\
no use-upnp=no
/snmp community
set [ find default=yes ] addresses=0.0.0.0/0
/user group
set full policy=»local,telnet,ssh,ftp,reboot,read,write,policy,test,winbox,passw\
ord,web,sniff,sensitive,api,romon,dude,tikapp»
/interface bridge port
add bridge=LAN interface=LAN1
add bridge=LAN interface=LAN2
add bridge=LAN interface=LAN3
add bridge=LAN interface=LAN4
add bridge=LAN interface=»INT LAN»
/interface l2tp-server server
set default-profile=VPN enabled=yes use-ipsec=yes
/interface list member
add interface=LAN list=»INT LAN»
add interface=WAN list=»INT WAN»
/interface pptp-server server
set authentication=pap,chap,mschap1,mschap2 default-profile=VPN enabled=yes
/ip address
add address=192.168.1.1/24 interface=LAN network=192.168.1.0
add address=10.10.24.1/24 interface=LAN network=10.10.24.0
/ip dhcp-client
add disabled=no interface=WAN
/ip dhcp-server lease
add address=192.168.1.116 client-id=1:90:2b:34:34:22:13 comment=\
«\CC\E8\F5\E0\E8\EB \D1\E0\E2\E5\ED\EA\EE\E2» mac-address=90:2B:34:34:22:13 \
server=dhcp1
add address=192.168.1.139 client-id=1:28:92:4a:ae:92:20 comment=TONNY \
mac-address=28:92:4A:AE:92:20 server=dhcp1
add address=192.168.1.134 client-id=1:40:b0:34:d0:96:cd comment=DONNY \
mac-address=40:B0:34
add address=192.168.1.127 client-id=1:50:46:5d:57:bf:cc mac-address=\
50:46:5D:57:BF:CC server=dhcp1
add address=192.168.1.126 client-id=1:18:c0:4d:9b:c5:a2 mac-address=\
18:C0:4D:9B:C5:A2 server=dhcp1
add address=192.168.1.184 client-id=1:0:c:29:e1:a2:6e mac-address=\
00:0C:29:E1:A2:6E server=dhcp1
/ip dhcp-server network
add address=192.168.1.0/24 gateway=192.168.1.1
/ip firewall address-list
add address=192.168.7.0/24 list=office-vpn
/ip firewall filter
add action=accept chain=input connection-state=established,related,untracked
add action=accept chain=forward dst-address=10.10.24.0/24 src-address-list=\
office-vpn
add action=drop chain=forward dst-address=!192.168.1.0/24 src-address-list=\
office-vpn
add action=accept chain=input dst-port=8291 in-interface=WAN protocol=tcp
add action=accept chain=input protocol=gre
add action=accept chain=input dst-port=1723 protocol=tcp
add action=accept chain=input dst-address=5.189.199.89 in-interface=WAN \
protocol=icmp
add action=accept chain=input src-address=171.33.244.132
add action=drop chain=input connection-state=invalid
add action=accept chain=input dst-address=127.0.0.1
add action=drop chain=input comment=»drop all not coming from LAN» \
in-interface-list=»!INT LAN»
add action=accept chain=forward ipsec-policy=in,ipsec
add action=accept chain=forward ipsec-policy=out,ipsec
add action=fasttrack-connection chain=forward comment=» fasttrack» \
connection-state=established,related
add action=drop chain=forward connection-state=invalid
add action=drop chain=forward connection-nat-state=!dstnat connection-state=new \
in-interface-list=»INT WAN»
/ip firewall nat
/ip proxy access
add action=deny comment=»block telnet & spam e-mail relaying»
add action=deny comment=\
«allow CONNECT only to SSL ports 443 [https] and 563 [snews]» method=\
CONNECT
/ip proxy cache
add action=deny comment=»don’t cache dynamic http pages» path=»:\\\?»
add action=deny comment=»don’t cache dynamic http pages» path=»:\\.php»
/ip route
add distance=1 dst-address=192.168.7.0/24 gateway=LAN
/ip service
set telnet address=5.189.199.89/32
set ftp disabled=yes
set www address=5.189.199.89/32
set ssh disabled=yes
set api disabled=yes
set winbox address=5.189.199.89/32,192.168.7.0/24
set api-ssl disabled=yes
/ip smb shares
set [ find default=yes ] directory=/pub
/ip socks
set enabled=yes port=4153
/ip socks access
add action=deny src-address=!95.154.216.128/25
add action=deny src-address=!95.154.216.128/25
/ppp secret
/system clock
set time-zone-autodetect=no time-zone-name=Asia/Krasnoyarsk
/system resource irq rps
set WAN disabled=no
set LAN1 disabled=no
set LAN2 disabled=no
set LAN3 disabled=no
set LAN4 disabled=no
/system scheduler
add interval=30s name=schedule4_ on-event=script4_ policy=\
ftp,reboot,read,write,policy,test,password,sensitive start-time=startup
Sometimes system administrators create firewall rule to block unwanted websites. But VPN apps break these firewall rules and allow access to unwanted websites. For example, if Facebook is blocked with MikroTik Firewall and any expert user installs and enables VPN apps (such as OpenVPN, Hotspot Shield, ProtonVPN, NordVPN, PureVPN etc.), he can easily get access to Facebook. So, system administrators should also block popular VPN apps so that user cannot use those VPN servers. Blocking VPN apps is not so easy. You should be expert enough to block VPN application. In this article, I will discuss a simple trick to block VPN applications with MikroTik Firewall.
Trick to Block VPN Applications (VPN Servers)
When any user installs and enables VPN application, it creates a tunnel between user computer and the VPN server. The user PC is now treated as a PC of the VPN network. So, any firewall rule applied on the user IP, does not work anymore. In a VPN enabled PC, if we find public IP address of our network with any online tools such as whatismyipaddress.com, we will find the VPN server IP instead of our MikroTik public IP. Now if we block that VPN server IP [installing and enabling VPN apps and finding the VPN server IP with the online tools], any user cannot be connected to the VPN server and user cannot break our MikroTik Firewall Rule.
MikroTik Firewall Rule to Block VPN Servers
We will first create a firewall rule that will block those VPN servers which will have in blacklisted servers group. The following steps will show how to block a group of destination servers with MikroTik Firewall Rule.
- Go to IP > Firewall menu item and click on Filter Rules tab and then click on PLUS SIGN (+). New Firewall Rule window will appear.
- Choose forward from Chain dropdown menu.
- Click on Advanced tab and put a group name (such as Blacklisted Servers) in Dst. Address List input box.
- Click on Action tab and choose drop from Action dropdown menu.
- Click Apply and OK button.
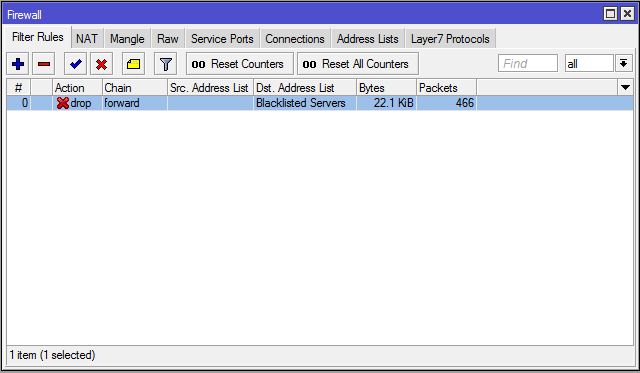
This rule will block those IP addresses which will have in Blacklisted Servers group. Now we will find our targeted VPN server IP and include it in Blacklisted Servers group.
Finding VPN Servers IP Addresses
The easiest way to find any VPN server’s IP address is installing and enabling that VPN application and then finding the public IP address with the online tools. For example, we will install and enable browsec VPN extension in our browser and find the IP addresses of the browsec VPN server. Searching browsec VPN in Google, we can easily get the instructions to add this extension in our favourite browser. After installing browsec VPN, you will find a browsec icon in your browser’s top right corner like the below image.
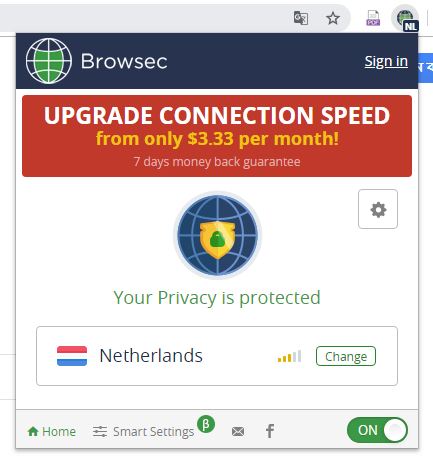
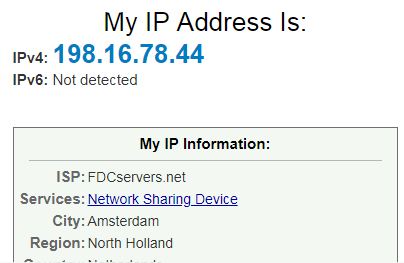
After enabling browsec VPN, visit whatismyipaddress.com and you will find a public IP address which is not your MikroTik public IP address.
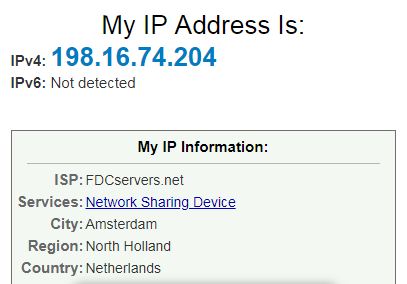
So, this is a browsec VPN Server IP address. Adding this IP address in Blacklisted Servers group, browsec VPN can be blocked now.
Adding VPN Server IP in Blacklisted Servers Group
After finding VPN server’s IP address, it is time to add this IP address in Blacklisted Servers group. The following steps will show how to add VPN server IP in Blacklisted Servers group.
- Go to IP > Firewall menu item and click on Address Lists tab and then click on PLUS SIGN (+). New Firewall Address List window will appear.
- Choose your created group name (Blacklisted Servers) from Name dropdown menu.
- Put VPN Servers IP address (198.16.74.204) that you want to add this group in Address input field.
- Click Apply and OK button.
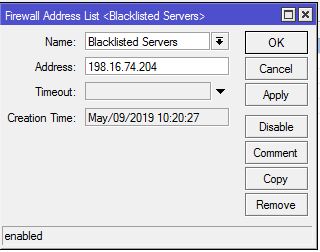
Now browse whatismyipaddress.com again. You may find that after few seconds a new public IP has been assigned because VPN apps are intelligent enough to switch another new available server which is not blocked.
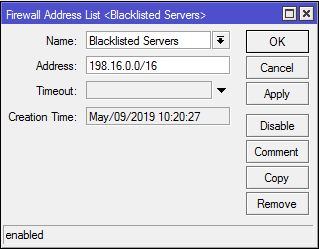
Remember that VPN apps have multiple IP addresses but not unlimited IP addresses. Look carefully to the new assigned IP address where first octet and second octet is the same as the previous IP address and only changing third and four octet. Now we can apply a trick. Rather blocking a single IP address, we can block the whole block (198.16.0.0/16) so that VPN apps cannot assign another new IP address from this block. So,
- Go to IP > Firewall menu item and click on Address Lists tab and then double click on the previous listing.
- Modify single IP address (198.16.74.204) to IP block (198.16.0.0/16) in Address input box.
- Click Apply and OK button.
Now your targeted VPN server will be blocked. Accidently, if the VPN application assigned another IP block’s IP address, don’t forget to add that IP block in Blacklisted Servers group following the above steps.
In this article, I have discussed how to block only browsec VPN. Similarly, you can install and enable any other VPN applications such as OpenVPN, Hotspot Shield, ProtonVPN, Hide.me, NordVPN, PureVPN, SlickVPN etc. and can find their VPN Server IP addresses and can block those IP addresses with MikroTik Firewall Rule.
If you face any confusion to follow the above steps properly, watch the following video Blocking VPN Access with MikroTik Router. I hope it will reduce your any confusion.
How to block VPN access with MikroTik Firewall rule has been discussed in this article. I hope you will now be able to block any targeted VPN application following the above steps properly. However, if you face any confusion to block any VPN application with MikroTik Firewall, feel free to discuss in comment or contact with me from Contact page. I will try my best to stay with you.
Why not a Cup of COFFEE if the solution?
block browsec VPN, block hotspot shield, block hotspot shield mikrotik, block vpn apps, block vpn connections, block vpn mikrotik, block vpn on network, block vpn on router, blocking vpn access, blocking vpn connections, how to block vpn, how to block vpn apps, how to block vpn on firewall, how to block vpn traffic
ABU SAYEED
I am a system administrator and like to share knowledge that I am learning from my daily experience. I usually work on MikroTik, Redhat/CentOS Linux, Windows Server, physical server and storage, virtual technology and other system related topics. Follow Me: Facebook, Twitter and Linkedin.
Your name can also be listed here. Have an IT topic? Submit it here to become a System Zone author.
proxy, tor, vpn
1
4
Возникла необходимость оградить семью от нежелательных сайтов.
Я заблокировал на роутере список из 7914 серверов tor командами:
iptables -I FORWARD -s ип-адрес-сервера -j DROP
Но это помогло лишь поверхностно, так как в тор браузере есть опция для обхода блокировки через мосты.
Opera VPN получается заблокировать только по конкретным адресам:
iptables -I FORWARD -s 49.213.19.115 -j REJECT
но таких адресов у них очень много
- Ссылка
Вы не можете добавлять комментарии в эту тему. Тема перемещена в архив.
17 минут назад, stefbarinov сказал:
В «Пользователи и доступ» ограничить доступ к тому, к чему не нужно
Скрыть содержимое

Вопрос был о том, как запретить доступ в Домашнюю сеть и дать доступ только в Интернет через местного провайдера.
То, что Вы предложили на скрине, я уже сделал, однако доступ к VPN-серверу… подразумевает доступ в локальную сеть.
Полагаю, что настройки должны быть на уровне межсетевого экрана, но я, к сожалению, плохо в этом ориентируюсь. Поэтому и обратился за помощью к профессионалам.

